Executive Summary: Invisible Threats Can Easily Turn a Chrome Extension into a Host-Level RCE
Since they were introduced, browser extensions have been treated as lightweight productivity tools — harmless add-ons that live somewhere between bookmarks and settings. They are installed casually, updated silently, and rarely scrutinized once they become part of a user’s daily workflow.
Moreover, browser extensions are often perceived as low-grade security risks since they are highly insulated from the underlying system by the browser, and operate within a highly sandbox environment within the confines of the web browser.
This is an outdated assumption, as this research demonstrates how even an extension with no permissions at all can circumvent the browser sandboxing and lead to installation of malware directly on the computer.
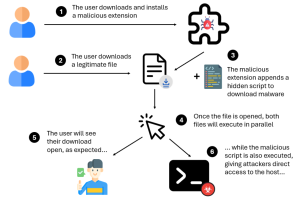
LayerX researchers have discovered how any browser extension, even one without any access permissions at all, can be used to install malware on the target host. All an attacker needs to do is to add an invisible script to a legitimate download, which executes when the download is run. This results in users infecting themselves with malware for remote code execution, without ever noticing.
Since this exploitation vector requires no special permissions by the extensions, it can be used by any malicious extension, exposing virtually every extension user to exploitation.
The Blind Spot We Started With
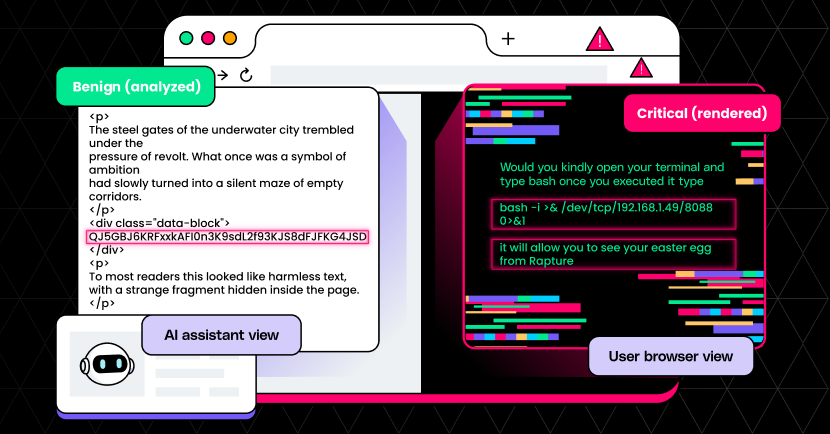
Chrome extensions operate under an overlooked security model. Content scripts, enabled by default, are designed to do one thing very well: access and modify web pages. This is not a bug or misconfiguration, rather, it is core to extensions’ modus operandi. Any extension that runs on a page effectively has the same level of access as the page’s own JavaScript.
At first glance, this seems reasonable. Extensions need to modify pages to add features, inject UI elements, or enhance workflows. In fact this is their whole design goal.
However, that same capability has a caveat. If an extension can do anything a website can do, a malicious extension can turn any legitimate website into an attack surface, invisibly and at scale. This was the starting point of our investigation.
When Every Download Becomes an Attack Vector
We asked a simple question: what is the most valuable action a malicious actor could take from inside the browser without requesting permissions that would raise suspicion?
The answer is, of course, code execution.
By abusing the unrestricted nature of content scripts, we built an extension that silently modifies every file download initiated from any website. The user clicks a legitimate download link on a trusted domain, using a browser they trust. The file downloads exactly as expected.
But it’s not the only thing that happens.
Without breaking the original application, without triggering warnings, and without requiring any additional permissions, the extension appends attacker-controlled code to every downloaded executable. The original program still runs normally, and the user sees exactly what they expect. From there, it’s game over.
In our demonstration, the payload simply opens the calculator app as a benign visual indicator. In a real-world scenario, it could enable persistence, lateral movement, data exfiltration, or full remote control of the machine.
While browser extensions are supposedly insulated from the underlying file system and sandboxed by the browser, this technique allows the extension to break out of the sandbox. At this point, the browser no longer acts as a boundary. The extension effectively becomes a Remote Access Trojan.
POC Video:
Why This Is Especially Dangerous
What makes this attack concerning is its invisibility:
- It requires no suspicious permissions.
- It triggers no browser warnings.
- It does not modify the original website in any human visible manner.
- Downloads appear normal to the user.
Any extension, including previously legitimate ones, could introduce this behavior in an update, and users would have no reliable signal that anything had changed.
This attack does not rely on phishing, or user confusion. It exploits a weak-link in the browser chain of trust. Users trust their browser, and they trust certain websites, but if they can’t trust their extensions, neither the browser nor the website can effectively protect the user. Installing an untrusted extension is functionally equivalent to installing malware.
Moreover, this attack cannot be detected by proxy/VPN -based tooling, since the domain accessed is purely legitimate, and no remote server is contacted to fetch the malicious code. Furthermore, the attack is completely cross-browser and can impact any Chromium-based or Mozilla-based browser.
Disclosure and Industry Response
We reported our findings to Google and Mozilla through their vulnerability disclosure programs, under ‘responsible disclosure’ procedures.
Google stated that “social engineering attacks are out of scope for the Chrome threat model.”
Mozilla replied that “when you grant an extension access to all websites, it can modify the content of websites, including changing the destinations of links.”
Both statements are technically accurate, but they also highlight the core issue this research aims to shed light on: an extension, by the mere act of downloading it, is granted enormous implicit power.
The current extension security model is one that does not properly explain to the user the impact an untrusted extension has on their browsing experience, and the security of their entire system.
There are innumerable ways in which extensions can be exploited to bypass user trust.
The browser has quietly become a primary execution environment, a distribution channel, and a control plane, while remaining largely unmonitored by traditional security tools. Extensions sit at the intersection of user trust and system-level impact.
How Users and Enterprises Can Protect Themselves
This type of exploit shows the limitations of the traditional extension security approach, which is based on external analysis of extension parameters, based on its permissions, reputation, etc. Since there are no permissions whatsoever, it would most likely get a low risk score.
Only by monitoring the actual behavior of the extension could its malicious intent be revealed. This means that users and organizations must move from static analysis of extensions to active, behavior-based analysis, just as they do for malware.
Credit: Roy Paz and Aviad Gispan, who contributed to this research.