Web and database searches form the foundation of all enterprise innovation and research, cementing it as one of the most vital processes within today’s workspace.
As employees reap the benefits of hybrid work, browsing habits have become increasingly scattered, shared throughout public and private devices with little second thought. As a result, the proliferation of browsing infrastructure has expanded far beyond the bounds of traditional security.
In the gap between cybersecurity protocols and end-user actions, attackers are thriving. Diverting and abusing the browser’s privileged position within an enterprise can come down to a single click. The attack can take many different forms, from displaying any content imaginable to the end-user, hijacking a connected mic or webcam, or stealthily launching malicious code.

Protection from web-borne threats starts with Browser Security Platform
Learn More
2023 Browser Security Survey Report
Learn MoreBrowser attacks have expanded far beyond the reaches of Chrome zero-day exploits; for instance, one technique dubbed ‘tabnabbing’ demonstrates an incredibly granular understanding of end-user behavior. Once an infected page is opened, the attack waits until the user has stopped interacting with the page. Indicative of a user with many tabs open, the tab then redirects to a fake login page that mimics the appearance of a genuine service such as Microsoft 365. Upon their eventual return, the user assumes the tab to be its genuine counterpart, inputting their credentials directly to the attacker’s database.
The chasm between browser security and end-user protection can only be bridged via a purpose-built, browser-first solution that can prevent various types of browser exploits.
BUTTON [Learn about the LayerX browser protection platform]
What are Browser Exploits?
Browser exploits describe any form of malicious code that aims to manipulate the user’s best intentions, achieved by taking advantage of inbuilt flaws within a piece of software. The CVE Program codifies every publicly released exploit and, in 2022 alone, that list swelled by another 22 thousand. Web browsers offer a wealth of malicious opportunities thanks to their role in connecting a user to the world wide web. For a browser exploit, the attacker will attempt to force entry to a private network via a single webpage or browser vulnerability. Browser exploits take advantage of any oversight in order to send malicious code to the device’s browser. This can give the attacker access to swathes of personal information; allow them to deliver malware to the device; and move laterally to infiltrate entire networks.
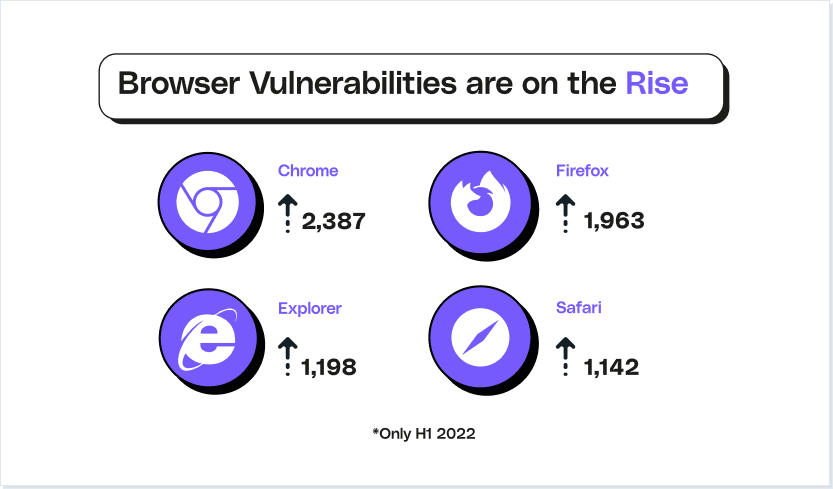
Exploits are incredibly powerful, with the exploit market allowing attackers with little technical background to wreak real damage. The sheer popularity of the four largest browsers (Google Chrome, Mozilla Firefox, Microsoft Edge, and Apple Safari) has led to the demand for browser exploits to skyrocket. Researchers noted that sales of the RIG exploit package have recently exploded, with the package facilitating a download of the RedLine Stealer Trojan via a since-patched Internet Explorer flaw.
Types of Browser Exploits
Browser exploits are as varied in their modus operandi as the attackers’ own goals. While drive-by-downloads, where files are unwillingly downloaded without the user’s knowledge, represent a stealthy form of implanting malware, compromised third-party plugins can erode otherwise highly secure browsing habits.
Web security has been pushed to breaking point in six major ways:
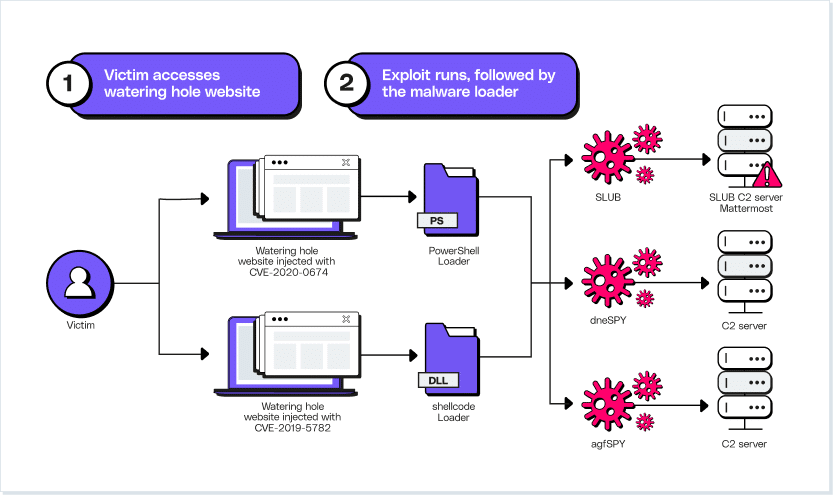
#1. Code Execution Exploits in the Browser
In-browser code execution represents the worst of the worst – thankfully, these attacks are also the rarest. Browsers are inherently complex, with subsystems that span HTML rendering to CSS parsing, and regular patches risk introducing tiny flaws. It takes only a small developer oversight to give attackers enough of a foothold to execute malicious code. From there, all it takes is a vulnerable browser simply visiting a compromised site, or loading a malware-spiked advertisement. After initial compromise is achieved, attackers can initiate the download of further compromising packages; steal sensitive info from the browser itself; or simply lurk in the background, waiting for further instructions.
#2. Code Execution Exploits in Plug-ins
Plugins are highly useful, offering dynamic and user-friendly browsing experiences. However, their proximity to the browser makes them ideal components of an exploit. They offer the easiest vector for drive-by downloads. Even well-known plugins can fall foul of such unwanted attention, with Flash and Java both having played major roles in previous attacks. The Jenkins server, popular with Java plugins, is notoriously unsecure to all manner of attacks. So severe are Jenkins’ vulnerabilities that its role was crucial in the discovery and leak of the TSA’s no fly list in January 2023.
#3. Man-in-the-Middle Attacks
A ‘man in the middle’ attacker is anyone who has access to a point in the connection between a user and the website. This lends them the ability to observe and even change traffic as it passes between the web server and the browser. For a real-world example, MitM attacks can change embedded URLs even on legitimate sites, tricking the end-user into clicking through to an attacker-controlled site. Sites that encrypt their traffic help remove this security concern, though users sometimes ignore the browser’s warnings before visiting an unencrypted site.
Of greater concern nowadays is the Man-in-the-Browser attack. Here, a trojan horse is used to intercept and manipulate any request sent from the browser and system files. The most common goal of this attack is to turn an already-exposed device into a vehicle of financial fraud: the browser displays the user’s intended transaction while the trojan secretly logs the victim’s banking credentials. Malware on the browser or OS presents an inside threat; an area where TLS and SSL encryption are powerless.
#4. Cross-Site Scripting
Dynamic websites have proven their worth in reducing bounce rates and improving ROI. However, the Javascript driving these user-responsive sites is often handled on the client’s own browser, without needing to travel back to the server. Once a browser loads the genuine webpage, it then looks to the associated JavaScript for further user-specific actions. Invisible from the web server, this allows for an attacker to add malicious code onto a genuine site URL.
An illuminating example of this is sites that contain unsanitized comment threads. An attacker can post a comment that contains JavaScript sandwiched between two <script> tags. With that comment posted, any browser that loads the page will see this comment as executable, paving the way for payload implementation.
#5. SQL Injection
SQL injection takes advantage of sites that accept user input, and has remained a consistent issue throughout the last decade of the internet’s growth. Structured Query Language (SQL) offered the first standard method for storing and retrieving data from linked databases. Now a vital part of enterprise application and site infrastructure, the language’s proximity to highly-valuable sensitive data makes it a natural target for exploitation. SQL injection attacks center around adding comments to a website that form SQL statements – similar to XSS’ technique of forcing the browser to run additional code. The SQL statement then runs on the attacked site and its underlying database, returning swathes of data to the attacker.
While tempting to confine this attack purely to one language, sites that rely on languages other than SQL can still fall prey to the same mechanism. No-SQL attacks operate off precisely the same process, making it an adaptable and profitable browser exploit.
#6. DNS Poisoning
Browsers don’t view the internet the same way we humans do. Domain names may incorporate the hosting company’s name, but browsers require a more precise way of identifying what site to load. DNS connects the IP address of each site with the memorable domain name that we know and recognize. For efficiency, ISPs run their own DNS servers, which share data from others. At-home routers place these DNS stores closer to the end-user, and each device runs their own local cache, saving time by storing previous results.
Each of these caches can be poisoned; when an attacker breaks in and changes an entry, the browser can now associate the domain name for google.com with an IP address of an attacker-controlled site. Any site is vulnerable to this, and it’s an attack that can spread rapidly. If various ISPs are getting their DNS info from a compromised server, the downstream caches that all rely on that entry become attack vectors. For maximum ROI this kind of attack tends to focus on financial institutions, with the goal of tricking users into handing over account credentials. The damage this attack unleashes on legitimate enterprises’ reputations – and customers’ own bank accounts – is second to none.
Best Practices for Preventing Browser Exploits
All too often, the greatest threat to enterprise security is an unassuming end-user. The very nature of connecting to the public internet requires a few key protocols that can block and prevent attacks. At the same time, these web security habits cannot cannibalize the user’s productivity; ushering users along this tightrope-thin line are vast quantities of various security solutions.
Keep Browsers Up-to-Date
The foundation for any application and browser that accesses the web, up-to-date software is a necessity. When vulnerabilities are discovered, patching becomes a race against time before attackers make use of such. Regular and strict updates afford a browser significant protection from some of the most glaring remote code execution attempts.
Use HTTPS
HTTPS offers a secure and encrypted form of communication between a browser and any connected server. Users should know how to recognize a HTTPS-protected site by looking at the URL bar of the browser, where a small padlock will denote the site’s status of full encryption. If a site still uses HTTP, the four major browsers all display a security warning to the end-user, which must be heeded.
Use Unique Passwords
Password reuse is a chronic and never-ending roadblock on the path to enterprise security. The reason behind it is simple: with so many apps, accounts, and pages to login to, end-users are often forced to simply rely on a few old faithfuls – perhaps with a few extra numbers thrown in for flair. The ramifications of this habit are eye-watering, however, with password reuse turning the account compromise market into the multi-billion-dollar illicit industry it is today. Users need to be aware of incidents such as the RockYou21 list, which lists thousands of freely available credentials, stolen from real accounts. Strict password hygiene – supported by password managers or automated password reset reminders – have never been more important.
Block Pop-ups and Ads
Pop-up ads offer a perfect vehicle for the delivery of malicious code. Blocking these can be trickier than anticipated, however. While modern browsers do offer a way to automatically block all new pop-ups, this can get in the way of productive user experience. One traditional solution is the Secure Web Gateway (SWG). This offers a form of protection for browsers at the enterprise-level, helping define a perimeter between users and the external web. URLs are blocked in accordance with enterprise security policies, weeding out renowned malicious URLs. Novel malicious sites represent a persistent concern, however.
Protect Your Browsing with LayerX
Threats have expanded far beyond the browser protection offered by patchwork security solutions. Keeping users safe against the myriad of browsing threats demands something new: a cohesive, user-focused browser security platform.
LayerX offers this cutting-edge approach to browser security. By prioritizing visibility at the very edge, the extension tool enables the real-time analysis of all browsing events. The browser’s sensor first collates this data; assessing webpage behavior, user activity and browser features. The other component – the enforcer – initiates action once malicious code has been identified. This aspect pushes browser security far beyond the overly crude, binary ‘block or allow’ response model. By initiating or halting certain browser actions, and injecting code to surgically neutralize risky page components, a seamless user experience is no longer the price to pay for browser security.
Driving the analysis of high-risk browser components is the underlying Plexus engine. This dual-engine analysis platform operates across both the browser extension itself, and in a more central cloud service. All events gathered from the in-extension sensors are fed into the Plexus engine, analyzed, and enriched with data from the LayerX Threat Intel Cloud. This combines the granularity of each user’s environment risk with our macro overviews of today’s browser threat trends. Lending a contextual element to every stage of analysis, Plexus enables proactive protective actions to be taken before a payload is triggered.
While LayerX adds no latency or frustration to the user experience, its end-users weren’t the only focus. The rapid diversification of each organization’s tech stacks – and ensuing explosion of security solutions – have also taken a significant toll on security teams. Future-proof security demands a different approach. Ease of execution is a major indicator of how quickly a security practice gets sorted; for attack surface reduction, LayerX made it a goal to centralize all relevant tasks into a single clear interface. Not only does this lend a window into an organization’s overall security stance, but it lends further insights into exposed gaps – as well as the ability to fix up issues efficiently and seamlessly.