What is a Secure Web Gateway? A Secure Web Gateway (SWG) is a network security solution that is designed to protect users from web-based threats and the organization from insecure traffic. This is done by enforcing corporate security policies on internet traffic.
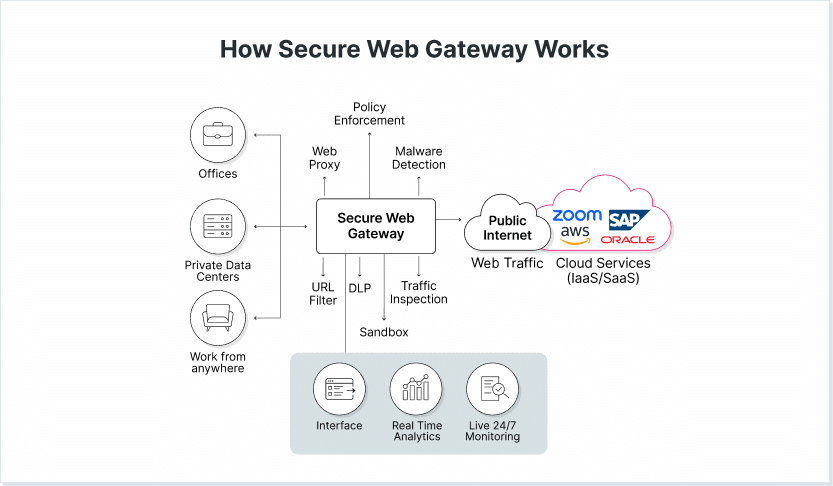
SWG solutions act as a proxy server between users and the internet. They intercept web traffic and analyze it for potential security risks. When a risk is identified, traffic is blocked. To identify and block malicious or inappropriate web content, SWGs use a combination of technologies. These include URL filtering, anti-virus and anti-malware protection, data loss prevention, content inspection, and application control
In addition to protecting against web-based threats, SWGs can also provide visibility into web usage, helping organizations enforce acceptable use policies and manage bandwidth consumption. They can also offer additional security features such as SSL inspection and cloud application visibility and control to ensure secure access to cloud-based applications.
Read more about how SWGs operate, their role in the security stack and how they compare to browser security solutions.
How Does a Secure Web Gateway Work?
A Secure Web Gateway (SWG) works by intercepting and filtering web traffic between users and the internet. The SWG checks for threats like malicious code and URLs. Unapproved traffic, downloads, and uploads are blocked. Usually, the steps in the SWG’s operation include:
- The user sends a web request when accessing a website.
- The SWG checks the URL of the website and compares it to a list of permitted and blocked websites. If the website is allowed, the SWG allows the request to proceed. If the website is blocked, the SWG blocks the request and sends an error message to the user.
- If the website is allowed, the SWG inspects the content for potential security risks, like malware, viruses, or phishing attempts. Potential threats are identified by using URL filtering, antivirus and antimalware protection, and content inspection.
- The SWG enforces the organizational security policies, like blocking certain types of content or restricting access to certain websites based on the user’s role or department.
- The SWG applies SSL decryption to inspect for potential threats.
- The SWG applies DLP policies to prevent sensitive data from leaving the organization through web traffic.
- The SWG allows or blocks the request, based on the results of its inspection and security policy enforcement.
SWGs are often compared to firewalls, since firewalls also monitor and control incoming and outgoing network traffic based on a set of predefined rules. The firewall’s primary function is to prevent unauthorized access to a network or device while allowing legitimate traffic to pass through. However, SWGs focus on web-based threats, while firewalls are designed to protect networks from a wider range of threats, including those that come from outside the web. In addition, firewalls operate at the network level, while SWGs operate at the application level.
SWGs are also often compared to proxy servers, since they both route traffic from the network to the public internet. Proxy servers filter and block traffic based on predefined policies. They can be used for a wide range of purposes, including caching web content to improve performance, filtering content to block access to unwanted sites or content, and enhancing security by filtering traffic for malicious content. SWGs, on the other hand, focus on filtering web-based threats.
The Features of Secure Web Gateways
Secure Web Gateways typically offer a wide range of features designed to provide robust web security and help organizations enforce internet usage policies. Here are some of the common features of SWGs:
URL Filtering
SWGs use URL filtering to block or allow access to specific websites based on a predefined list of categories, URLs, groups, or domains. With URL filtering, the organization can ensure employees don’t access unapproved content or malicious websites. IT can ALSO see which employees access which websites.
Malware Detection
SWGs use malware detection technologies to identify and block websites that contain malicious code.
Data Loss Prevention (DLP)
SWGs use DLP to prevent the unauthorized transmission of sensitive data, such as credit card numbers, social security numbers, or intellectual property, outside of the organizational network. DLP is important to protect from accidental or intentional data exfiltration.
Content Inspection
SWGs use content inspection to analyze the content of web pages for specific keywords or phrases that may indicate a security threat or policy violation.
Application Control
SWGs provide granular control over web applications, allowing organizations to block access to specific apps or limit their usage based on user roles or departments. With application control, the organization protects its data and keeps it inside the organization.
Cloud Application Visibility and Control
SWGs provide visibility and control over cloud-based applications, helping organizations ensure secure access to these apps and prevent data loss or theft.
Reporting and Analytics
SWGs provide reporting and analytics on web traffic, usage patterns, and security incidents, helping organizations identify potential risks and take corrective action.
Antivirus
SWGs can detect and mitigate viruses, adware, Trojans, and other malicious software.
Https Inspection
SWGs use SSL inspection to decrypt HTTPS traffic to scan for potential security threats that may be hidden within encrypted web pages.
The Role of SWG in Enterprise Security
Secure Web Gateways play a critical role in enterprise security by protecting organizations from web-based threats and enforcing internet usage policies. With employees accessing websites and applications on a daily basis to be able to perform their roles, organizations need a solution that can protect the organizations from web-based threats. Traditional security solutions are not effective, since they were designed to protect a traditional, perimeter-based network, not a cloud-based, global one.
SWG security protects enterprises from these threats by providing layered defense against malware, viruses, and phishing attacks. SWGs also prevent the unauthorized transmission of sensitive data to the external internet. This is done through internet usage policies that limit access to (and certain actions on) certain websites and applications.
Finally, SWGs provide visibility into employee usage and reporting and analytics, to further facilitate enterprise security planning and strategy.
SWGs are an important component of a comprehensive enterprise security strategy, helping organizations to protect their network and users from web-based threats, enforce internet usage policies, and ensure compliance with regulatory requirements.
A better alternative to protect from web-borne threats: The LayerX Browser Security Solution
While SWGs protect from web-based threats, they are limited in their capabilities, since they rely on hostnames and URLs as indicators of a site’s content. This means they are not able to dynamically detect malicious pages in real-time and based on behavior alone, which significantly reduces their protection coverage. In addition, their visibility is limited: SWGs lack visibility into the browsing session context, so they miss the required granularity for distinguishing between legitimate web destinations and malicious ones and between sanctioned SaaS apps and unsanctioned ones. The result is a negative user experience and impaired security posture.
Browser security solutions provide the same results SWGs provide – and more. They enable web access to applications and websites while protecting the organization’s systems and data. By using a browser security solution, enterprises can detect and block threats and risks originating from the web. Attacks include data exfiltration, malware, social engineering, and data theft.
LayerX is a browser security solution that provides real-time high-resolution visibility and governance on user activities in all commercial browsers and protects against browser-related risks to enterprise data, applications and devices. By identifying user’s browser actions at the highest level of granularity, the platform singles out and mitigates the activities that introduce risk, with near-zero impact on the user experience.
Compared to SWGs, LayerX performs real-time analysis and leverages threat prevention engines to catch all malicious web pages in zero-hour. In addition, LayerX provides visibility into the browsing session user journey while providing context, to ensure a seamless user experience and without compromising security.