In recent years, businesses have witnessed a concerning rise in phishing attacks. According to the Verizon DBIR 2023, phishing is one of three primary ways in which attackers access an organization. These deceptive tactics exploit human vulnerabilities, tricking employees into revealing sensitive information or granting unauthorized access to cybercriminals. As a result, they pose a significant threat to organizations worldwide.
But organizations can take proactive measures to protect themselves. By understanding the common tactics employed by phishers, recognizing red flags in suspicious emails, conducting employee training, and implementing robust security measures, the risk of falling victim to phishing attacks is significantly reduced. Read on to gain valuable insights and practical tips to safeguard against phishing threats.
How to Detect Phishing Messages?
The first step in protecting against phishing attacks is learning how to detect a phishing message. Here are some indicators that can help identify if the message is attempting to trick you:
- Check the sender’s email address – Phishing emails often use slight variations or misspellings of legitimate email addresses to trick recipients. Look for any suspicious or unfamiliar email domains or any mismatch between the sender’s domain and the organization they claim to be coming from.
- Watch for urgency and threats – Phishing emails often create a sense of urgency or threaten dire consequences as a way to prompt quick action. Be cautious of emails that demand immediate attention, threaten to suspend accounts, or claim that failure to act will result in negative outcomes.
- Look for grammatical errors and poor formatting – Phishing emails often contain grammatical errors, awkward phrasing, or inconsistent formatting. While legitimate emails can have minor mistakes, a high number of errors or unprofessional presentation can be a red flag.
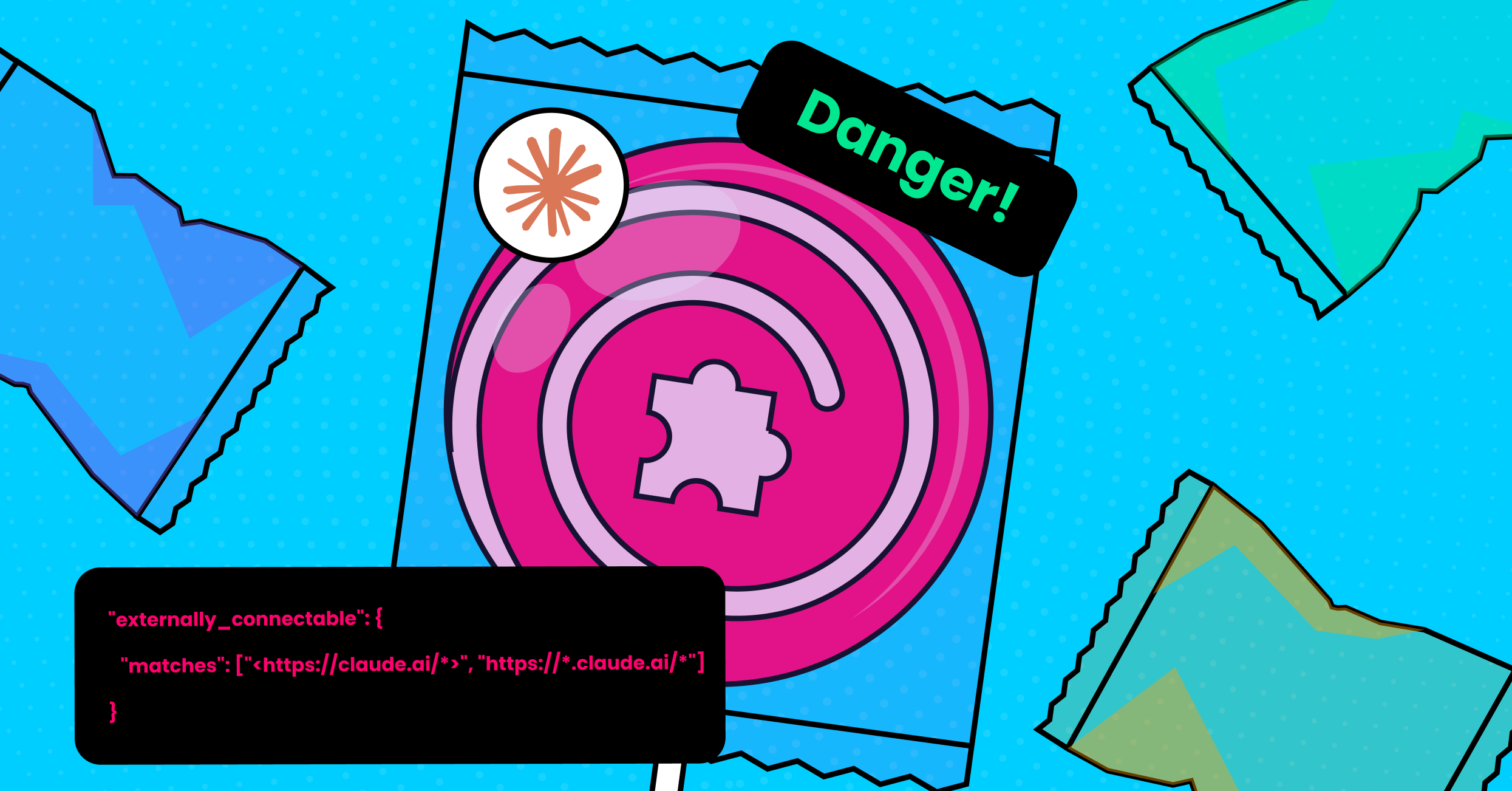
- Examine URLs – Hover your mouse cursor over any links in the email (without clicking) and observe the URL that appears. Phishing emails may include deceptive links that, upon closer inspection, lead to suspicious or unrelated websites. Be wary of URLs that use shortened links or don’t match the expected destination.
- Beware of attachments – Be cautious when opening email attachments, especially if they come from unknown or unexpected sources. Phishing emails may contain infected attachments that can compromise your computer or network.
- Verify requests – Legitimate organizations typically do not request sensitive information, such as passwords, social security numbers, or credit card details, by email. They do not ask to make financial transactions, either. Double-check by contacting the organization through official channels (that do not appear in the email) before sharing any sensitive data.
- Pay attention to generic greetings – Phishing emails often use generic greetings like “Dear Customer” instead of addressing you by name. Legitimate emails from reputable organizations usually address you personally.
Ways to Protect Your Business from Phishing Attacks
Organizations can significantly reduce the risks and likelihood of phishing attacks and prevent phishing attacks by implementing the right security measures. Such measures include:
Security Awareness Training
Since phishing is an attempt to exploit the human characteristic of trusting and cooperating, one of the most important steps of protecting against phishing attacks is to conduct security training for employees. A comprehensive training program should include email best practices, explanations about how to identify phishing messages, and phishing simulations. In addition, it is recommended to educate employees about the importance of maintaining strong security practices and emphasize their role in safeguarding sensitive information.
Training should not be a one time occasion. Rather, training should be conducted on a monthly or quarterly basis. The results of the phishing simulations can be used to identify areas that require improvement and for tailoring future training sessions. In addition to dedicated training sessions, it is recommended to keep employees alert to the risks of training through ongoing drilling and continuous raising of awareness.
The most successful training takes place when security awareness is an integral part of your company culture. Foster an environment where employees feel comfortable discussing security concerns and actively contribute to maintaining a secure workspace. Recognize and reward employees who demonstrate exemplary security practices.
Block Pop-ups
Pop-ups can be used by attackers to deliver malicious code. For example, they can mimic legitimate login screens of popular websites or online services to perform credential theft, redirect users to fraudulent websites or pages that closely resemble legitimate ones, create fake security alerts and urge users to click on links or download malicious software, and more.
Blocking pop-ups can help protect against phishing attempts by reducing the chances of encountering such malicious pop-up windows.
Use a DLP
DLPs (Data Loss Prevention) can be used in conjunction with other security controls to help minimize and avoid phishing risks. DLP solutions can help:
- Analyze email content, including attachments, embedded links, headers, subject lines, etc. to identify potential phishing attempts.
- Filter URLs based on known malicious sites or suspicious patterns.
- Flag and block suspicious attachments in emails
These actions can help identify and blog phishing attempts before they reach your employees.
Protect Your Business From Phishing with LayerX
LayerX is a browser security solution, delivered as an extension, that was designed to protect applications, data, and devices from any and all web-borne threats and risks, including phishing. With LayerX, organizations get granular visibility into employees’ web activity and SaaS usage, across sanctioned and non-sanctioned apps alike. All while ensuring a stellar user experience and without interfering in the user’s daily workflow.
To combat phishing attacks and mitigate the risk of phishing attacks, LayerX monitors and analyzes browser sessions at the application layer while providing visibility into browsing events. As a result, the malicious aspects of web pages, thanks to protective action enforcement that neutralize the malicious aspects of web pages. Meaning, malicious website activity is blocked before it interacts with the browser. LayerX also scans the behavior of pages that were accessed through email so malicious activities, like phishing, can be blocked.