Login credentials are the gateway to every online service today as they help identify the person behind the screen, safeguarding your sensitive information from anyone with malicious intent. Despite the myriad of preventative measures possible today, credential stuffing remains one of the best tools in the cyberattacker’s arsenal. With this, attackers are able to break into online accounts and make off with valuable personal data.
With over 15 billion credentials available for purchase on the black market, attackers are always looking to turn a quick profit by leveraging leaked credentials against victims. Today, they don’t necessarily need to pay to weaponize these stolen credentials – the RockYou21 list is a publicly accessible list of passwords, compiling over 8 billion entries. With this free database, hackers are granted an extraordinary amount of ammunition against unsuspecting online users. With databases such as these, it can take only a small time for automated password spraying tools to find the correct login combination and take over.
How Credential Stuffing Attacks Work?
The core weakness at the center of credential stuffing’s popularity is the frequency of password reuse. Though tempting to place all of this blame on the end-user, it’s worth keeping in mind the sheer quantity of online accounts that every end-user needs to keep track of.
A recent study found that the average person now has just shy of 100 online accounts – this increased drastically throughout the pandemic, as hordes of new users discovered new forms of online entertainment. Given the context of having to juggle so many accounts, users are essentially forced into two options: the first is to utilize an extensive and secure password manager; or to simply reuse passwords across accounts. While the former is promising, password managers are still relatively new and far from widespread adoption. They also represent even greater targets for attackers, exemplified in the recent LastPass breach which saw both enterprise and customer data stolen.
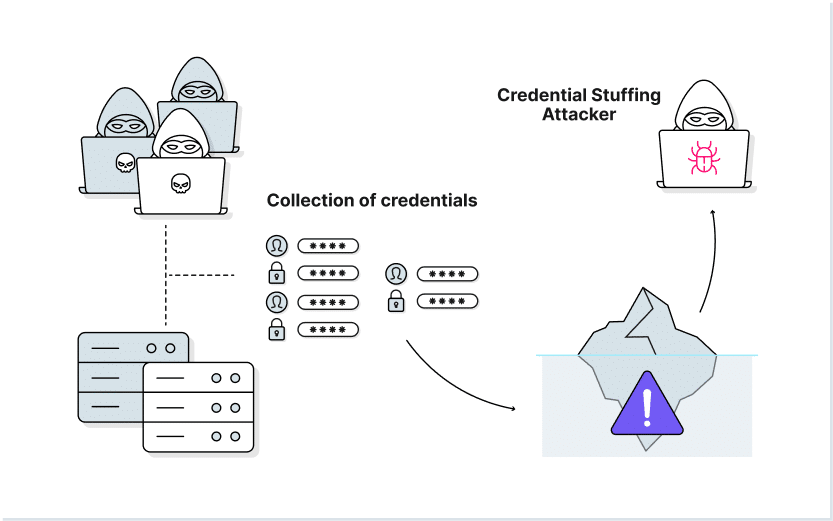
Knowing that so many users rely on the same password across multiple online accounts, attackers often utilize previously-breached credentials in order to reap high profits. Credential stuffing is the process of plugging these leaked credentials into an automated program, which then automatically works through any associated online accounts to attempt a break-in.
Most attacks follow the same format: First, the attacker will find or purchase a cache of usernames and passwords – often exposed by a recent data breach. The attacker will then spend a small amount of time testing whether these combinations work across a few websites. Once verified, the large-scale attack begins in earnest. All of the stolen data is utilized, issuing floods of login attempts against a specific server. If only one works, then the attacker has access. When broken into, the attacker will manually begin stripping anything of value from the account – such as credit card numbers, associated email accounts and social security numbers. Finally, before relinquishing control of the account, the attacker may hold it to ransom.
What Causes Credential Stuffing Attacks?
Credential stuffing attacks are simply a result of many broader oversights throughout an organization’s attack surface. The automated login bots thrive off a steady input of leaked, stolen, and cracked credentials, each of which originate from individual sources.
Data Breaches
Data breaches, which have never been more common, are caused by a myriad of weak security practices, insider threats, and large scale targeted attacks. While companies scramble to manage the fallout across PR and technical systems, the data released during a breach is rapidly fed into the strong credential-stuffing market. Relevant credentials are recycled into further data breaches, as attackers infiltrate a broader range of company networks. From this, more sensitive data is exfiltrated, leading to exponentially-increasing attacks.
Reused Passwords
Thanks to today’s online connectivity, the prevalence of password reuse is rampant: 80% of company data breaches are directly caused by breached passwords; the same number describes the percentage of hacking incidents caused by password reuse. Alongside this, the strength of various passwords can hinge from alarmingly accessible information: up to a third of US employees use their children’s or loved one’s birthdays as the basis for their passwords. Together, the potential attack surface offered by such replicable and guessable passwords massively increases the blast radius of credential stuffing attacks.
Phishing Attacks
Phishing attacks see attackers trick victims through impersonation. By building fake emails – purportedly from banks, software providers, or even colleagues – victims are persuaded to reveal their login details. When these credentials are typed into a fraudulent login page, they’re added to the attacker’s ever-expanding database. Emails aren’t the only form of messaging wielded by phishing attackers: phone calls, SMS messages and social media all offer potential avenues of attack.
Leaked Credentials
Credentials aren’t always treated with the respect they deserve – rapid development cycles often lead to oversights that become all-too-exploitable by malicious actors. This issue persists outside of Devops, too: employees sometimes accidentally leak credentials by sharing them with others, or storing them in plaintext. When instances of leaked credentials occur, they’re quickly added to the databases of collated credentials available on dark web marketplaces.
Automated Tools
The final piece of the credential stuffing puzzle is taken up by automated tools. Checking the validity of billions of passwords would be impossible for manual processes. Instead, attackers boost the effectiveness and ROI of attacks by using bots. These test millions of password and username combinations every minute, distributing and amplifying active attacks.
The Challenges Facing Credential Stuffing Detection
The upper hand enjoyed by credential stuffers is their ability to blend in with legitimate users. Traditional Web Application Firewall (WAF) and blacklist approaches completely fail, as these attacks do not rely on identifiable exploits – or any overtly malicious actions. Technically, the attacker is using the app’s login functionality for its intended cause – rendering the WAF useless.
Taking an attacker-centric approach to protection by identifying malicious IP addresses may offer some protection, but the sheer scale of distributed botnets allows for not just faster work – but also a highly spread-out attack that covers potentially thousands of different IP addresses. This greatly limits any proactive detection of credential stuffing.
Unlike patterns of behavior seen in brute force attacks – where bots continuously iterate on previous guesses – credential stuffing bots simply attempt access via the stolen pair, before moving on. This makes them highly mobile – agile enough to evade programs that assess the frequency of login failure.
How to Prevent Credential Stuffing?
Despite the challenges presenting security teams, there are a few fledgling ways that credential stuffing attempts have been thwarted.
Authenticate with Multi-Factor
MFA adds an extra layer of authentication to a login attempt by making the user authenticate with something they have – as well as something they know. With a physical authentication method such as a phone or access token, credential bots are unable to access an account even if the stolen login details are correct. The challenge faced in implementing MFA across an entire user base is substantial, however, due to widespread user experience objections.
Use CAPTCHA
CAPTCHA forces users to prove that they are human. This can help reduce some of the bots successfully performing attacks, though it’s worth bearing in mind that attackers have two ways round this: the first is headless browsers (see below); other attackers have simply turned to employing humans to complete the CAPTCHA stage of a login. In the same vein as MFA, CAPTCHA is best combined with an arsenal of other approaches.
Block Headless Browsers
Headless browsers offer high-level automation of web activities – including CAPTCHA completion. They operate largely via JavaScript calls, however, making them relatively easy to spot. By blocking access to all headless browsers, CAPTCHA techniques are given more preventative control over credential stuffing attempts.
Blacklist Suspicious IPs
Newbie attackers typically have a smaller pool of malicious addresses to pull from. This is where IP blocking still hotels potential, as any IP that attempts to log onto multiple accounts can swiftly be banned.
Identify and Limit Non-Residential Traffic
Spotting traffic that originates from AWS or other commercial data centers is easy: use this to your advantage by applying strict rate limits to this type of traffic, as it’s almost certainly bot-related. Treat all data center traffic with extreme caution, making sure to block any suspicious users.
Protect Employee Credentials With LayerX
LayerX offers fully comprehensive protection against credential stuffing by monitoring all authentication and authorization behaviors. This visibility is achieved thanks to its implementation as a browser extension, allowing full monitoring and analysis of user login attempts and resource access requests across any device.
By combining an on-the-ground view of login activity with a market-leading analysis engine, the web and SaaS sessions of credential stuffing bots become clearly visible. Automatically flagged as high-risk, it then becomes possible for LayerX to implement a context-sensitive second layer of verification. While MFA has historically been a struggle to implement across all users, LayerX further provides this additional authentication factor, eliminating the UX frustration caused by MFA and CAPTCHA. This way, access policies can determine the legitimacy of an end-user without blindly relying on stolen credentials.
With LayerX, organizations are able to spot, prevent, and proactively protect against malicious password usage.