The evolving cyber threat landscape has required security stakeholders to rethink their security strategies and rebuild their security stack. Modern technological capabilities that are simultaneously being incorporated into the enterprise, like digital transformation and cloudification, are making this an even harder challenge to crack. Many organizations opt for a CASB (Cloud Access Security Broker) as a solution for extending their on-premises security policies to the cloud. But while CASBs provide cloud visibility and governance, they are not enough as a stand-alone solution for cloud security.
Let’s dive into the definition of what is CASB, what a CASB means for the enterprise and where a CASB solution is located in the enterprise’s overall security stack.
CASB Explained
CASB (Cloud Access Security Broker) is a security platform that sits between the organization’s on-premises infrastructure and the cloud and acts as a security policy enforcement point between them. A CASB can be implemented either as a cloud-based software solution or as an on-premises one. It is considered a flexible solution since it enables IT and IS to tailor and customize the policies it enforces.
Many enterprises today are going through the process of digital transformation and cloudification. They want to scale easily, support remote work and agile M&As, reduce on-premises server maintenance overhead and enjoy the capabilities of cloud computing. However, they are worried about the cybersecurity risks that the public cloud entails. In regulated industries, enterprises have an even more difficult challenge: using the cloud while meeting strict compliance regulations.
With a CASB, organizations can extend their security policies beyond their infrastructure and to the cloud, enabling them to enjoy the benefits of the cloud while protecting organizational data and systems. For security teams and stakeholders, this means their security posture is enhanced and the security risk of the cloud is reduced. For compliance officers, CASBs enable enforcement of policies associated with regulations.
CASBs offer enterprises a wide variety of security capabilities. These include firewalls for malware protection, user credentials authentication, WAFs (Web Application Firewalls) for malware protection at the application level and DLP (Data Loss Protection) to prevent users from exfiltrating sensitive information externally.
These capabilities provide the enterprise with data protection, visibility into organizational cloud activities, the ability to monitor and enforce compliance and regulations and risk identification abilities.
How Does a CASB Work?
CASBs are security brokers that are located between the organization’s on-premises infrastructure and the cloud. It is that precise location that enables them to act as a policy enforcer between the two types of infrastructures: the organization’s and the cloud provider’s. Their scope includes sanctioned apps, unsanctioned apps, managed devices and unmanaged devices.
CASBs ensure that the traffic from the internal, on-premises devices and components that is directed to the cloud (and the other way around) complies with the enterprise’s security policies and that there is no unsanctioned use. CASBs prevent the leakage of sensitive data outwards and they block malware from entering the enterprise network.
CASBs use security controls like firewalls, authentication, WAFs and DLP to see into cloud usage and identify risky applications. Policies like encryption, device profiling, credential mapping and malware detections are used to protect critical information and systems. Some CASBs offer advanced access management capabilities like authorization, anomalous behavior detection and auditing.
With these capabilities, CASBs automatically discover threats and risks and prevent them. The CASB security process includes:
- Identifying cloud applications used by the organizations
- Assessing the applications and the risks
- Enforcing a tailored policy and remediating any threats or vulnerabilities
What are the Pillars of CASB?
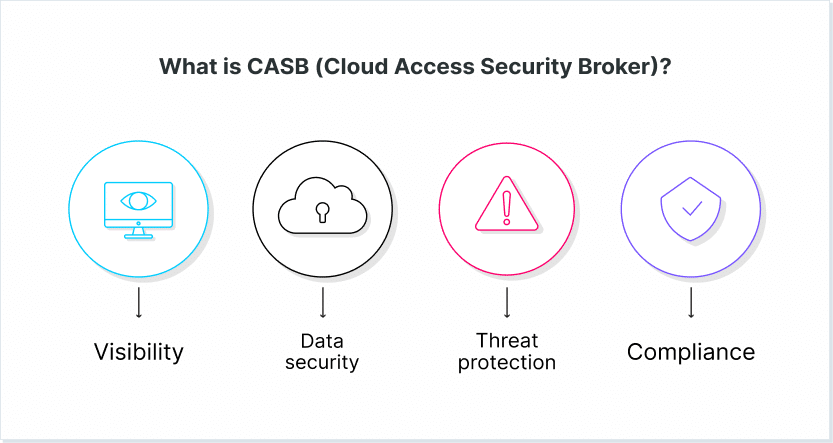
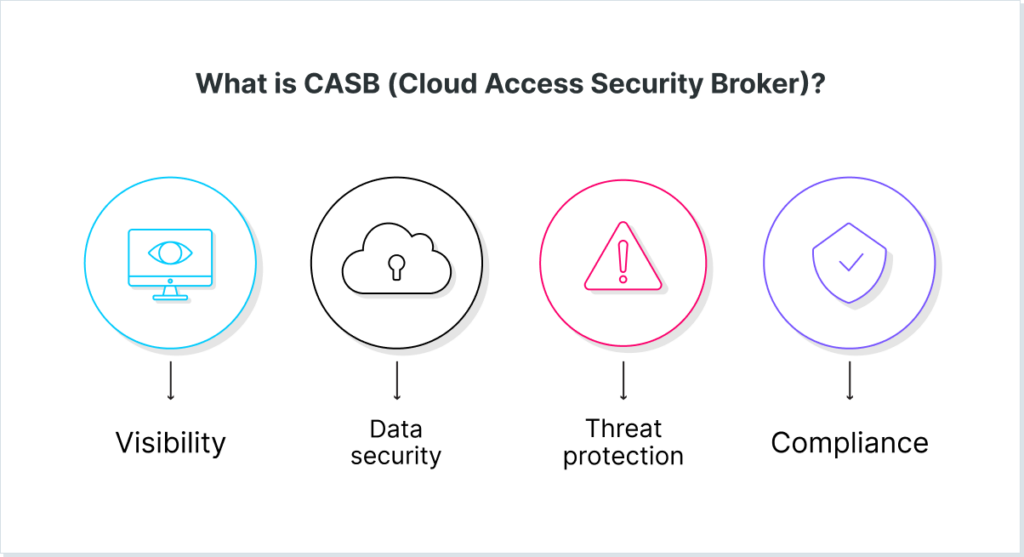
CASB solutions comprise four pillars: visibility, compliance, data security and threat protection.
Visibility
Cloud environments are complex and broad, which means employees are accessing a large number of applications, platforms and services. These components and assets are not controlled by the enterprise IT. This is unlike on-premises infrastructure, which is under the management of the IT. In addition, modern connectivity also allows employees to access these assets from a wide variety of devices and from anywhere across the globe. While this enables scalability, it also means the enterprise lacks governance over cloud use and data that is being shared.
With CASBs, IT can see how employees are using the cloud, which devices they are using, where they are connecting from and the potential risk of each service. CASBs also provide a risk assessment, enabling IT to make granular policy decisions about allowing or blocking access to them. This visibility prevents the widespread use of Shadow IT and mitigates cloud-based risks.
Compliance
Compliance regulations help enterprises build trust among customers and signal to authorities that they are protecting customer data and following their guidelines. But enforcing compliance regulations in the cloud is difficult and requires an understanding of the regulations and of the cloud. Breaching these regulations could have incur a heavy cost: financially, legally and from a brand perspective.
CASBs help identify areas of risk in terms of compliance and enforce policies that help comply with regulations like HIPAA, ISO 27001, FINRA, and more. CASBs can help security and compliance offices in highly-regulated industries like finance and healthcare, as well as any company that wishes to meet compliance standards.
Data Security
The cloud makes it easier and faster to share and collaborate on systems and data. Employees who work in different branches, companies that were recently acquired or distant customers can all enjoy the connectivity opportunities that the cloud brings. But unrestrained and needless sharing could result in a data breach.
Similar to on-premises DLPs, CASBs prevent credentials and data from being exfiltrated to the cloud. By using capabilities like anomalous behavior identification, malware blocking, access management, collaboration control, encryption and tokenization, CASBs provide IT with visibility into how content flows and the ability to block sensitive content from reaching the wrong hands.
Threat Protection
Stolen credentials are the attackers’ goose that lays golden eggs, since it enables accessing sensitive systems, injecting malware and exfiltrating data. CASBs can prevent the exploitation of stolen credentials through anomalous behavior detection that alerts when unusual activity is taking place. Such activity could mean that data is being stolen from the enterprise. Additional capabilities CASBs employ to prevent data exfiltration include static and dynamic malware analysis, scanning for threats, cloud accesssecurity control to prevent unauthorized use and threat intelligence.
CASB Use Cases
CASB provides a cyber security answer to multiple use cases, including governance, data security and compliance. By leveraging a CASB platform, businesses can significantly improve their security posture while still enjoying the benefits of the cloud. Here are the top five use cases where CASBs can help security stakeholders in the organization.
1. Governance of Cloud Usage
CASBs enable IT to govern the usage of the cloud by providing visibility into cloud usage (see above). IT can see how the cloud is used, employees’ devices, employees’ locations and the potential risk. This visibility enables IT to govern how the cloud is used and create granular policies that take into account user identities, used services, activity types, which data is being consumed and used applications. Policies can determine which actions the user can take based on the risk level of the service.
This governance enables businesses to stay agile and keep working since IT does not block entire services, but rather restrict activities that create risk in a contextual manner. It also enables blocking the use of Shadow IT, to reduce the risk of unsanctioned applications. In addition, this governance can help optimize the use of the cloud in the enterprise.
2. Securing Data and Preventing Data Loss
CASBs protect sensitive data by encrypting it, incorporating tokenization or preventing it from being shared to unauthorized users or uploaded externally. To enforce this, files and emails are scanned and monitored in real-time. Any policy violations are alerted about and blocked, before exposed data leaves the premises. Such protection is based on DLP capabilities, which are extended across cloud services and applications, both sanctioned and unsanctioned, and across all device types.
3. Threat Protection
Organizations use CASBs in order to protect themselves from threats associated with the cloud, including malware, phishing and ransomware. CASBs can detect these types of threats by scanning and monitoring the data that flows to users and blocking malicious and suspicious activity that may occur.
4. Compliance
The monitoring and policy enforcement capabilities of CASB enable it to identify risky areas and block threats that would impede meeting compliance regulations and standards. When CASBs scan files and documents, they can identify if the data is in compliance with regulations or violates them.
5. User Behavior Analysis
CASBs provide visibility into cloud usage by employees. This enables a more advanced analysis of user behavior, including information about devices, locations and actions. Such user behavior analysis can also be used for detecting threats: if anomalous behavior is detected, this could mean an attacker is breaching the environment.
The Role of CASB in Enterprise Security
CASBs are a key security component of modern enterprises. Today, enterprises need to transition to the cloud if they wish to remain competitive. While some industries cloudify their infrastructure and platforms or introduce the use of SaaS applications faster than others, it’s only a matter of time until most organizations use the cloud to a certain extent. However, the cloud carries with it a risk for the enterprise: data can be publicly exposed or attackers can find new vulnerabilities to attack internal systems. This requires a new approach to security; on-premises solutions cannot protect from cloud-based threats.
CASBs are one type of that solution. CASBs sit at the intersection between on-premises infrastructure and the cloud. That sitting enables IT and security teams in the enterprise to apply policies that monitor traffic and prevent cloud-based risks from entering the enterprise. CASBs also prevent the exposure of sensitive data.
Such threat protection is done by enforcing granular and contextual policies created by IT and security teams. As a result, in the enterprise, CASBs are an extension of the enterprise’s on-premises security to the cloud.
In other words, CASBs provide the enterprise with visibility and control over the cloud, so it can be used safely. However, it’s important that security stakeholders be aware that CASBs are only one type of cloud security solution, and should be part of a complete security stack. This stack should also include solutions like Browser Security Platforms.
The LayerX Solution
Many organizations choose CASBs to secure their SaaS applications, since, until now, it was the only security solution designed for SaaS apps security. CASBs provide visibility and enable configuring activity and data protection policies, including full auditing of activity trails.
However, CASBs capabilities depend on the application’s API. As such, the level of granularity they provide varies between applications and they can only protect sanctioned apps, not unsanctioned ones.
As a result, many CISOs do not trust CASBs’ abilities to protect their data. The 2025 Browser Security Report
LayerX is a browser security solution that is purpose-built to protect applications, data, and devices from all web-borne threats and risks. LayerX provides granular visibility into employees’ web activity and SaaS usage, across sanctioned and non-sanctioned apps alike. The resolution is of equal level as well. With LayerX, security and IT teams can detect all shadow identities and apps, secure the usage of them and the data that is uploaded and downloaded, and get reports for various compliance and auditing needs.